This guide walks you through setting up and running your first pentest with Cerberus.Documentation Index
Fetch the complete documentation index at: https://docs-cerberus.c7-security.com/llms.txt
Use this file to discover all available pages before exploring further.
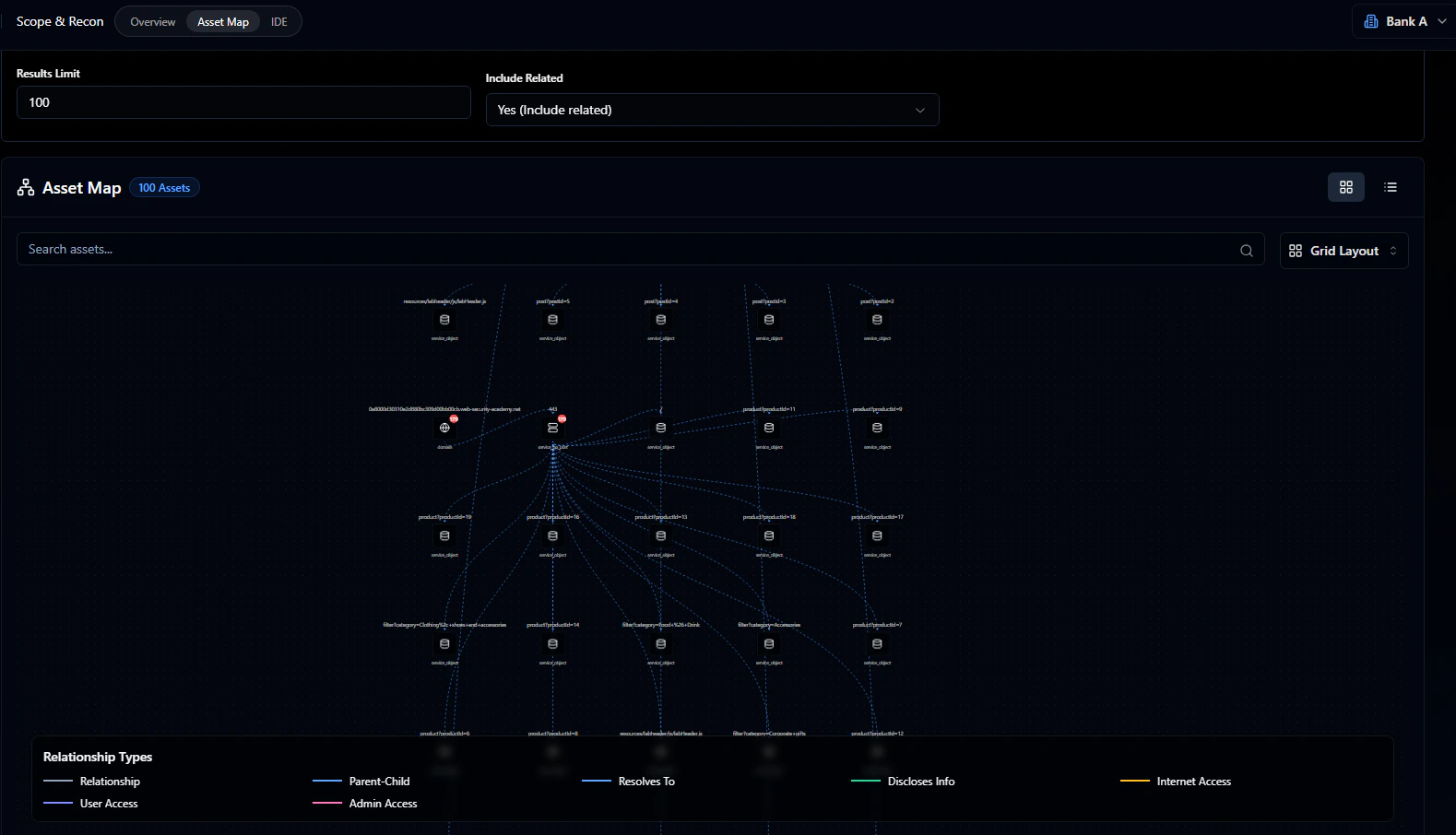
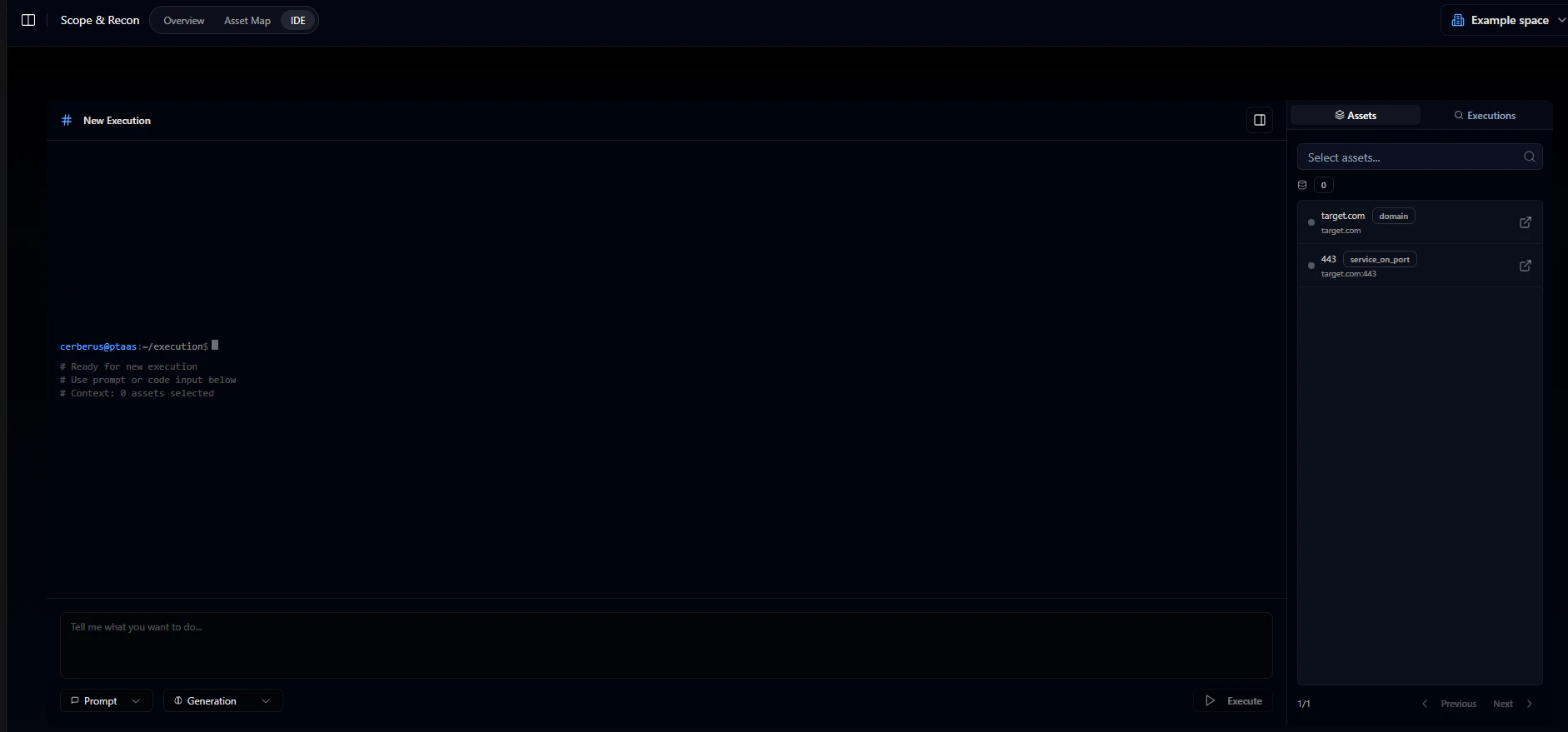
Step 1: Access the Scope and Recon tab
After logging in, go to the Scope and Recon tab. This is where you define your target assets. Once the pentest starts, you’ll see real-time updates here: assets being tested, vulnerabilities found, and attacks that were blocked.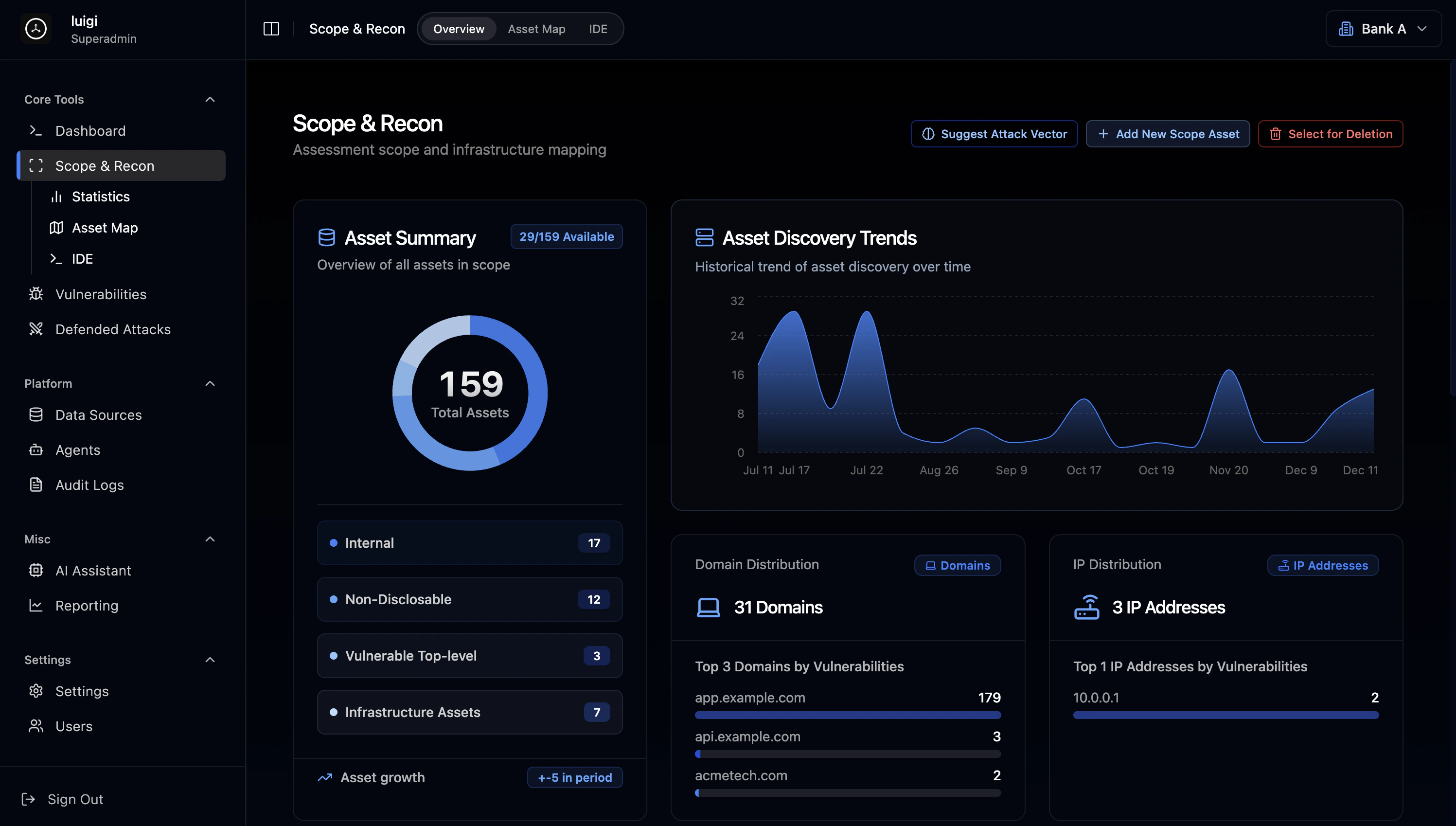
Step 2: Define your scope and add target assets
Click “Add New Scope Asset” on the right side of the page. You can add:- Domains (e.g.,
example.com) - IP addresses (e.g.,
10.0.0.1) - Services (e.g.,
http,https,ssh,ftp) - People (e.g., security analyst, developer) - they can be targets of social engineering attacks
- Objects (e.g., files, API endpoints, subfolders)
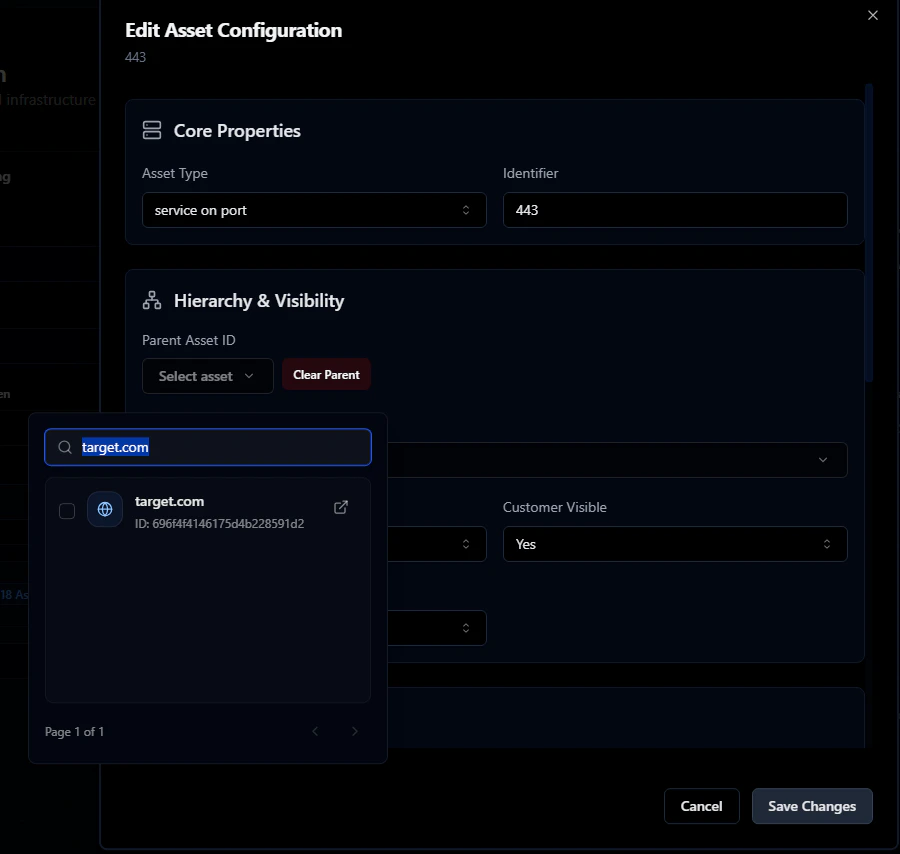
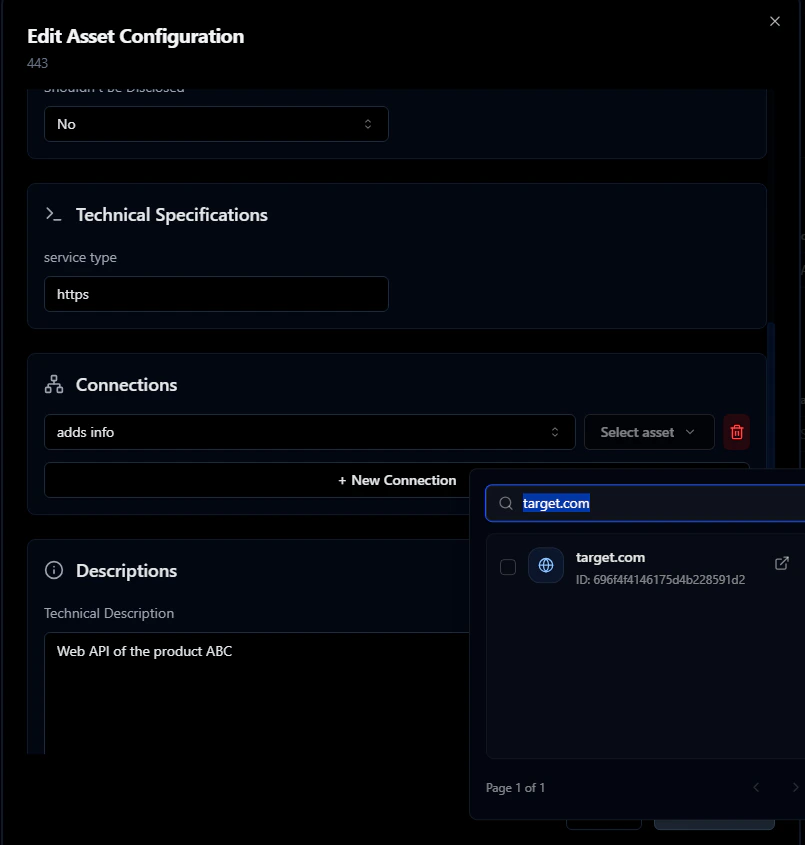
target.com and an HTTP service on port 443.
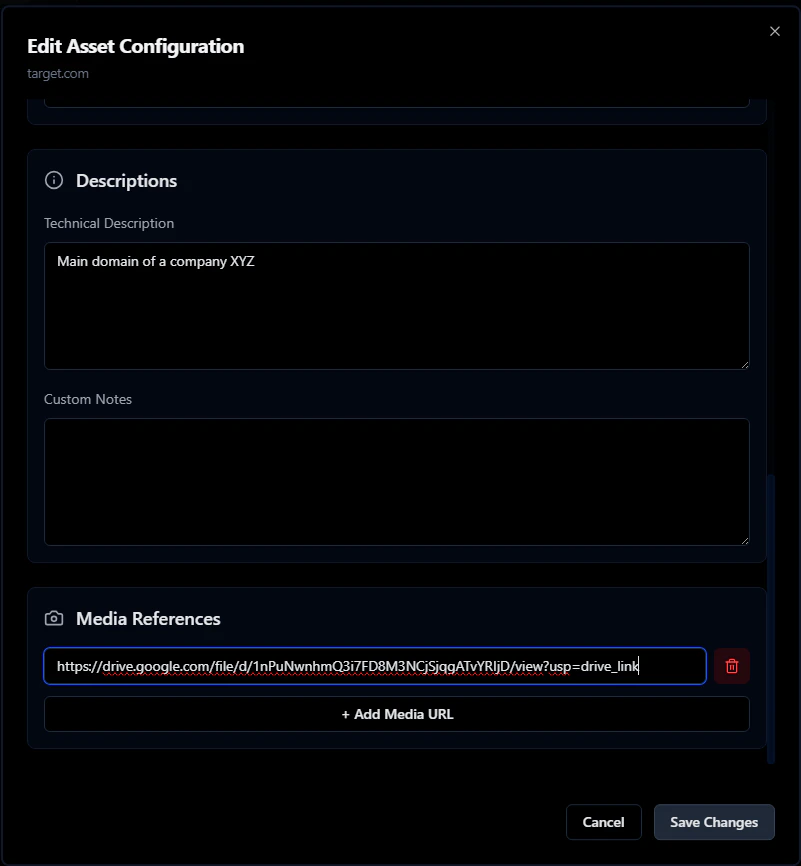
Fill in the other fields too: DNS system, relationships between assets, screenshots, etc.
Start with the domain target.com:
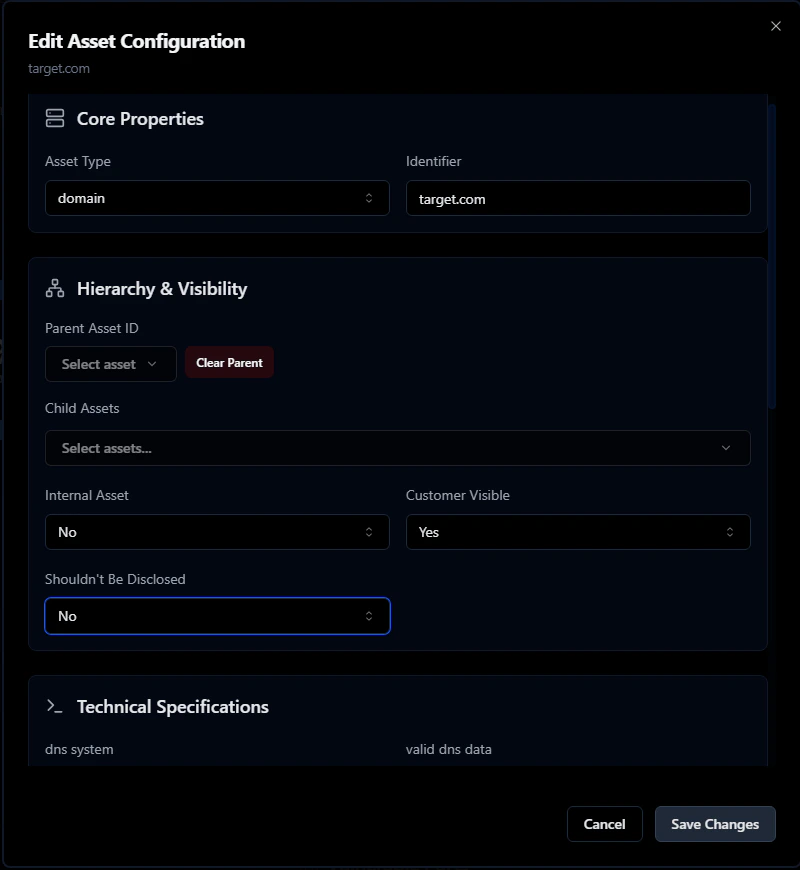
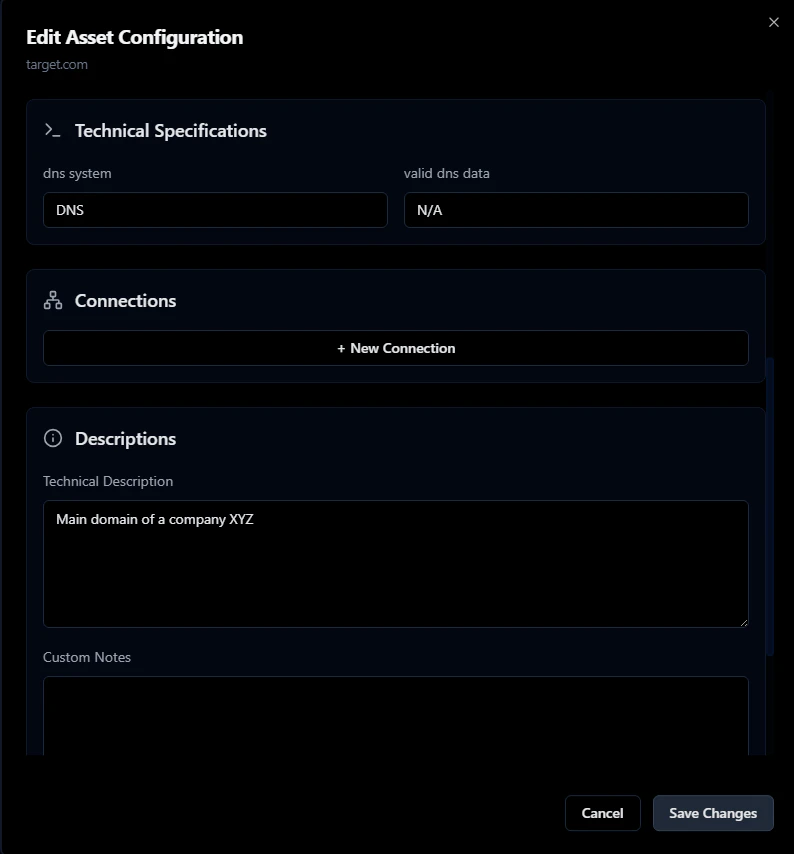
target.com as the parent - this links the service to its domain.
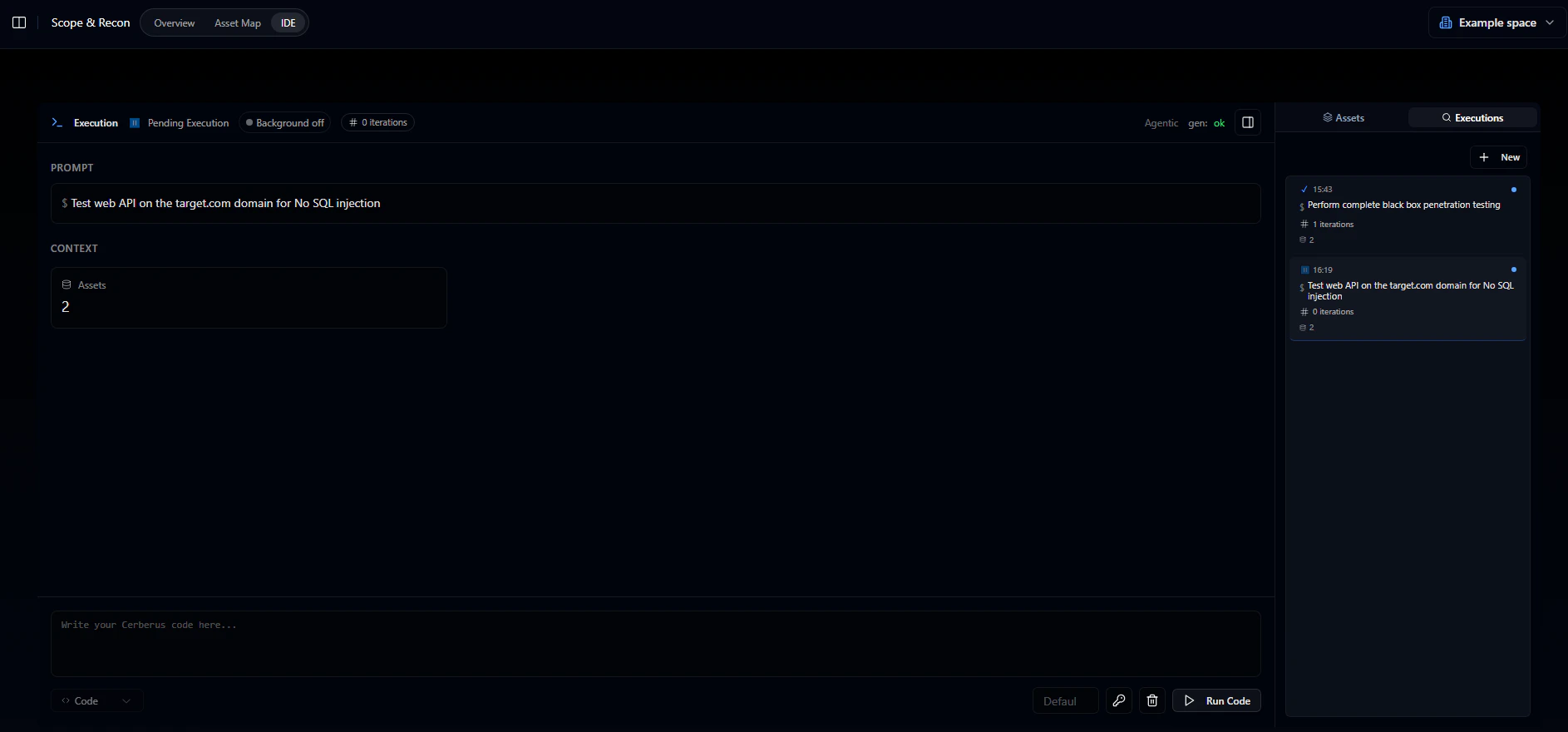
Step 3: Run your first prompt
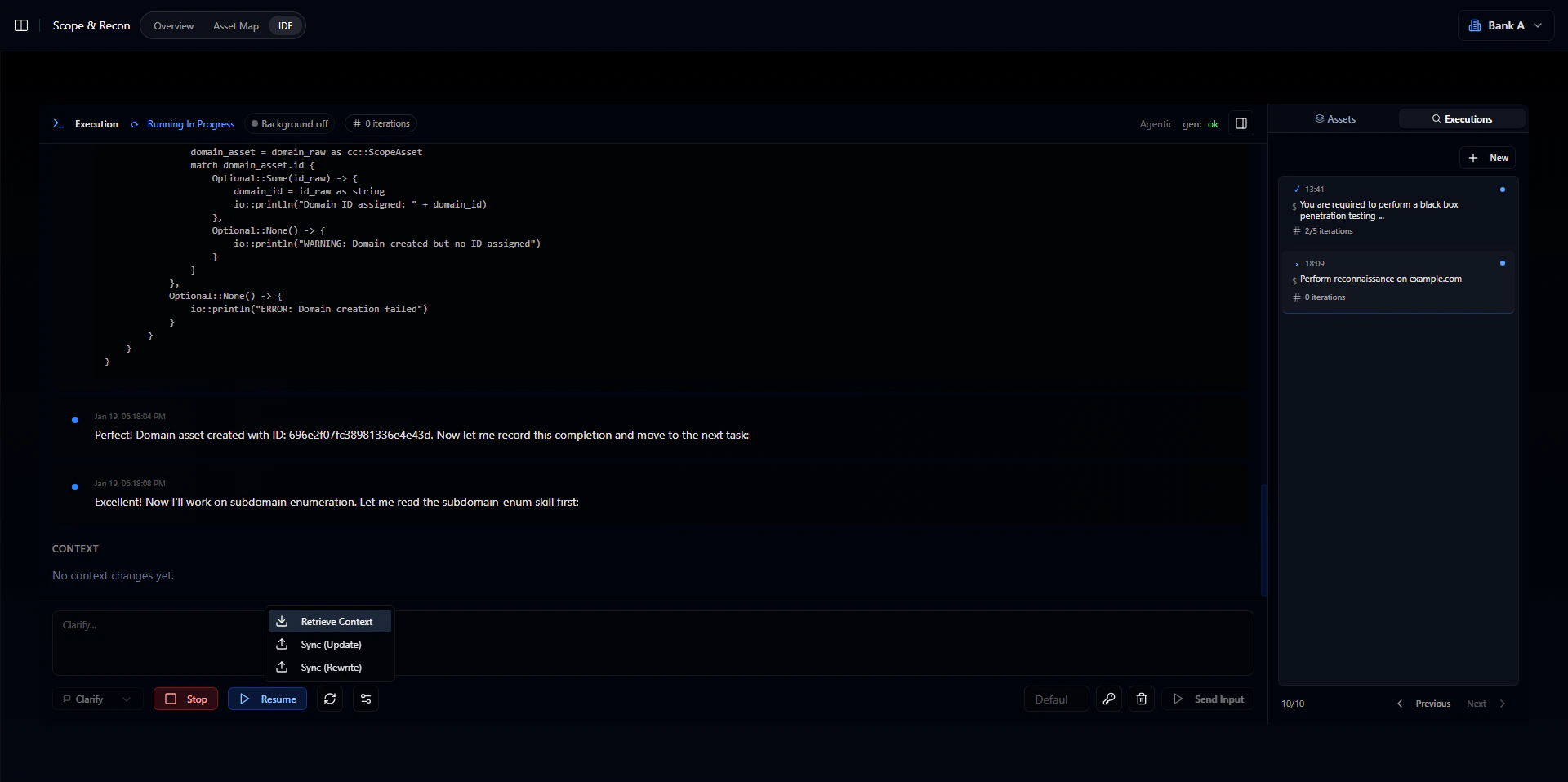
Go to the IDE tab within Scope & Reconnaissance. From here you can:- Generate automated scanning scripts
- Run automated pentesting with AutoPT
- Get AI-suggested attack vectors
- Click New Prompt
- Switch the selectors to prompt and pentest in the bottom left corner
- Write your instruction - for example, ask AutoPT to test a web API for NoSQL injection

- Max iterations: How many iterations AutoPT will run. Set this to around 50 for larger projects.
- RID: Runner ID - a unique identifier for the runner executing your code. Leave blank to auto-generate.
- Click the key icon
- Click Issue runner token
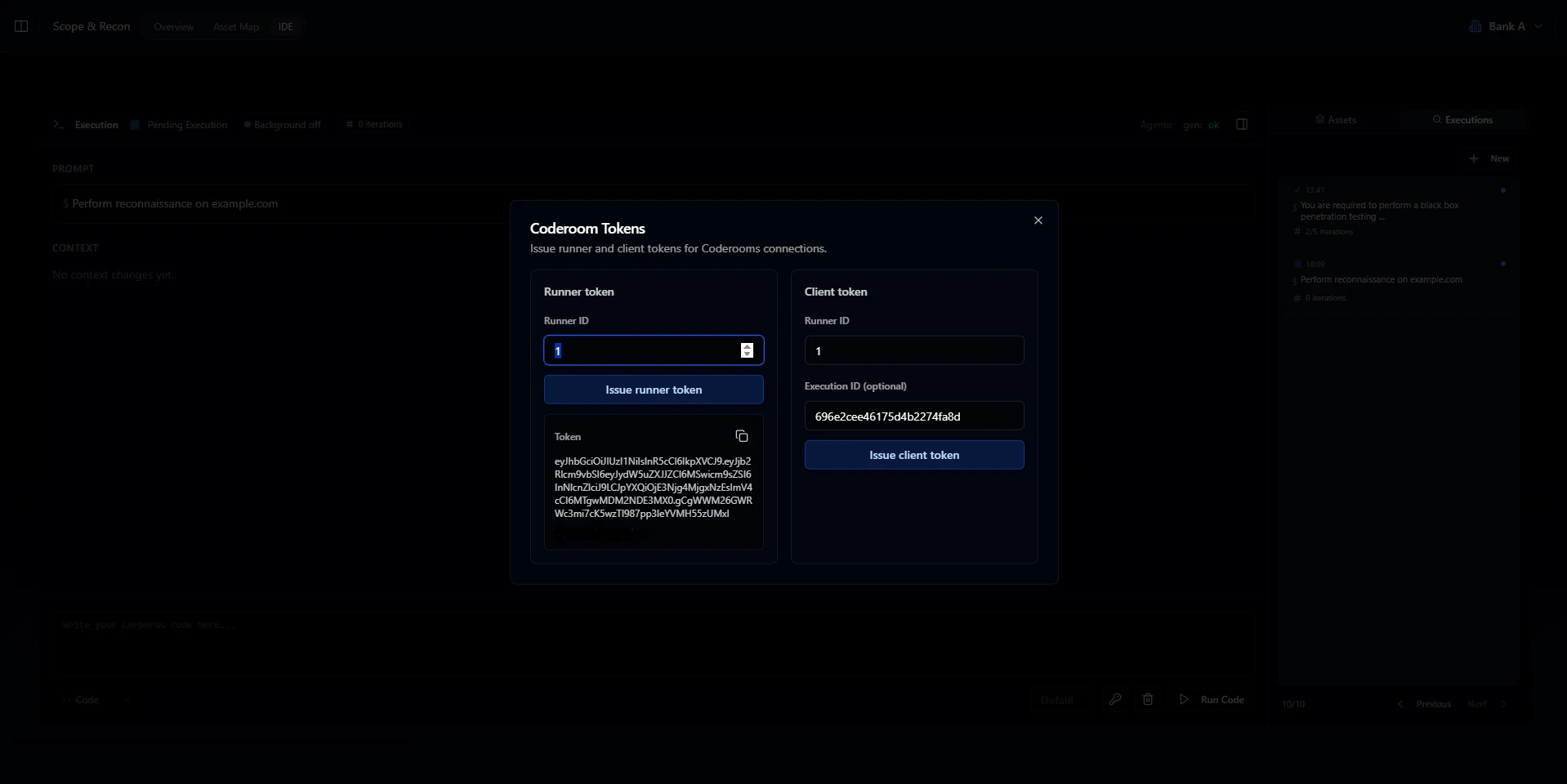
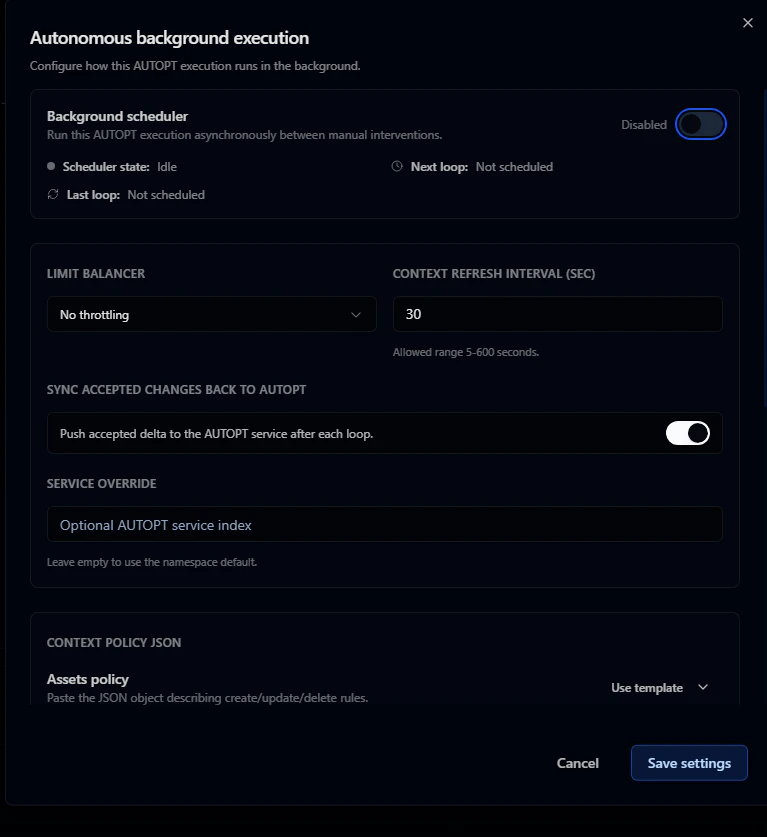
- Time intervals between iterations (to avoid rate limits or system overload)
- Scheduling (business hours only, specific days of the week)
- Maximum iteration count
- Whether to auto-apply context changes
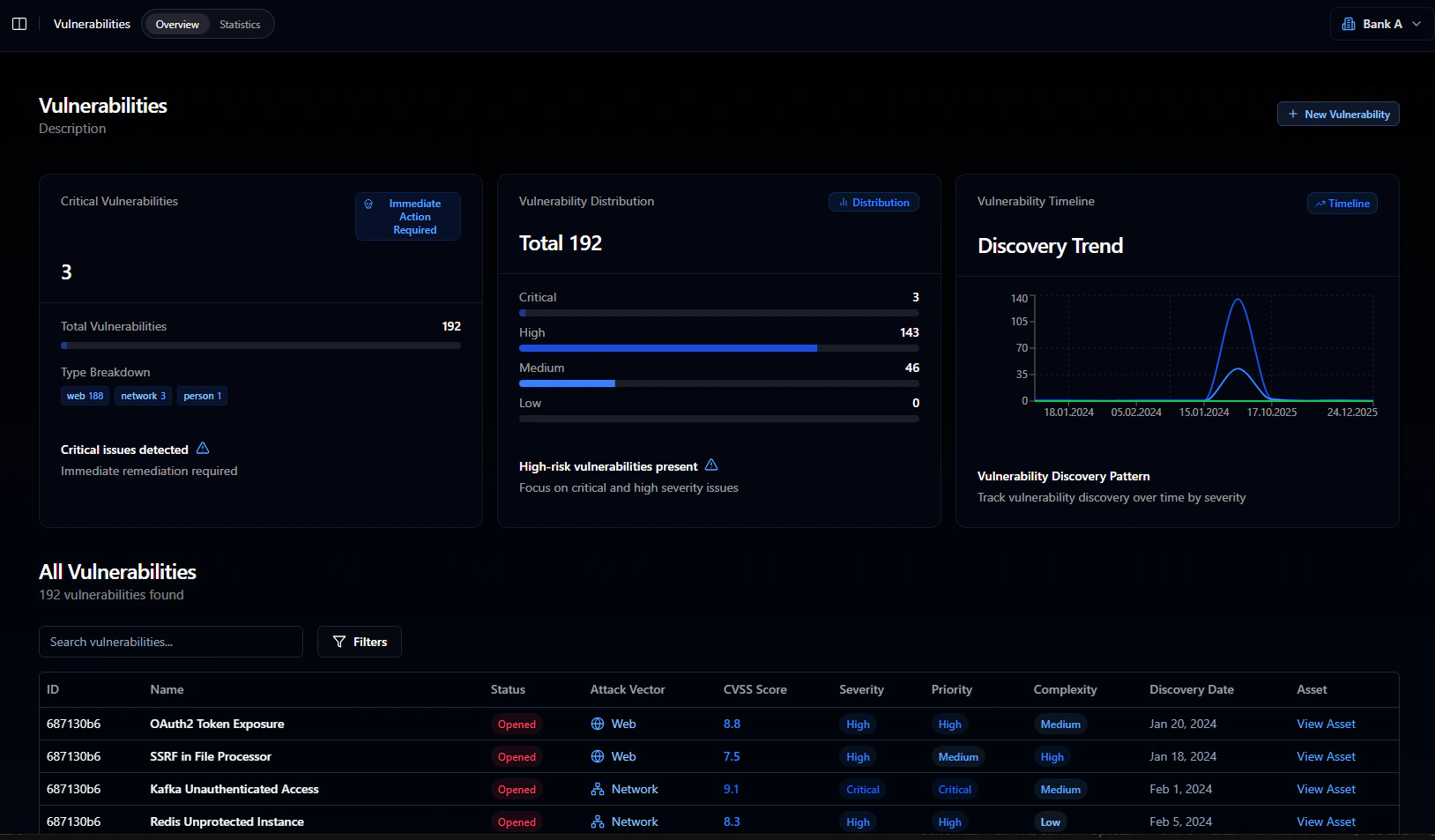
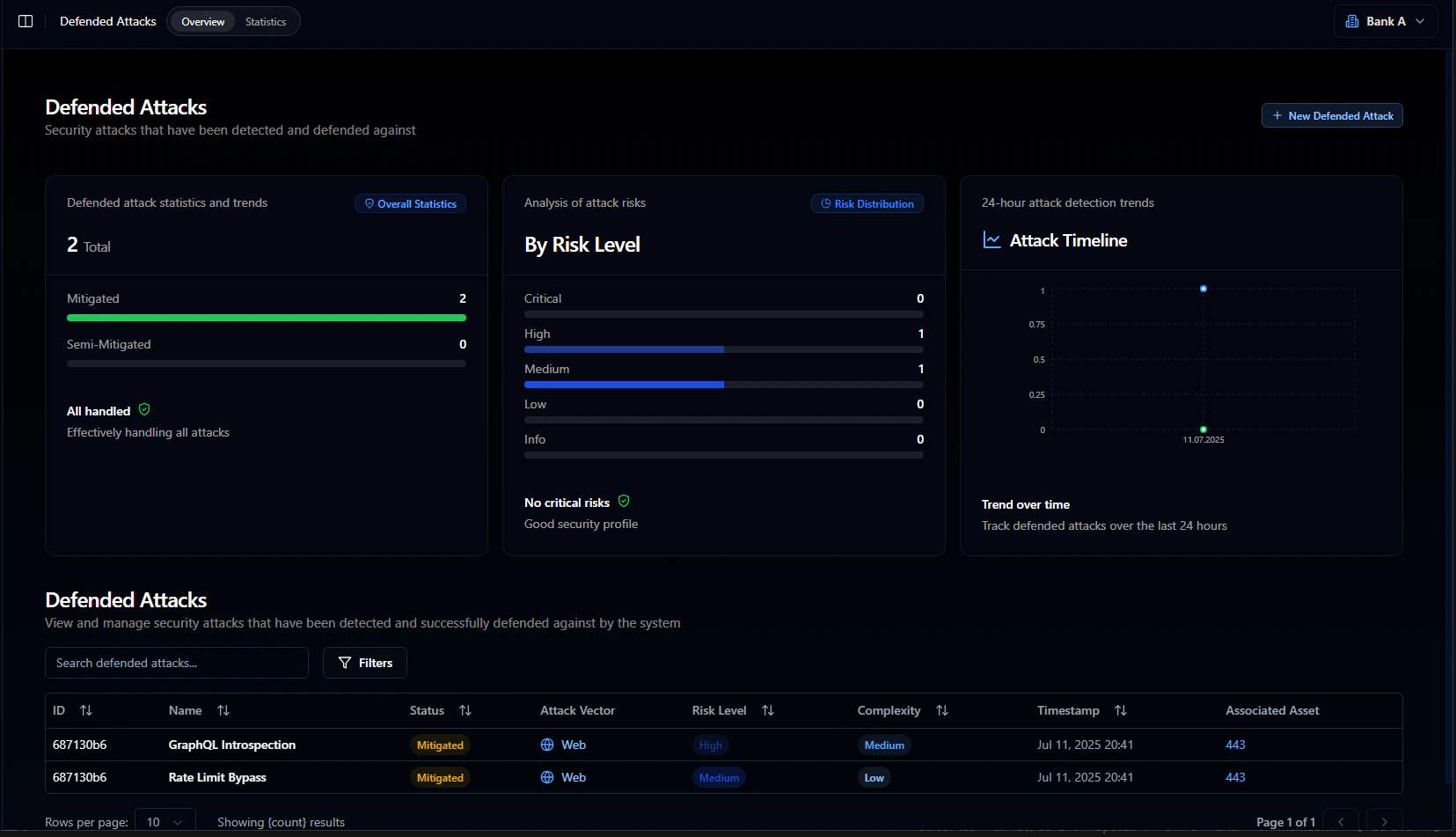
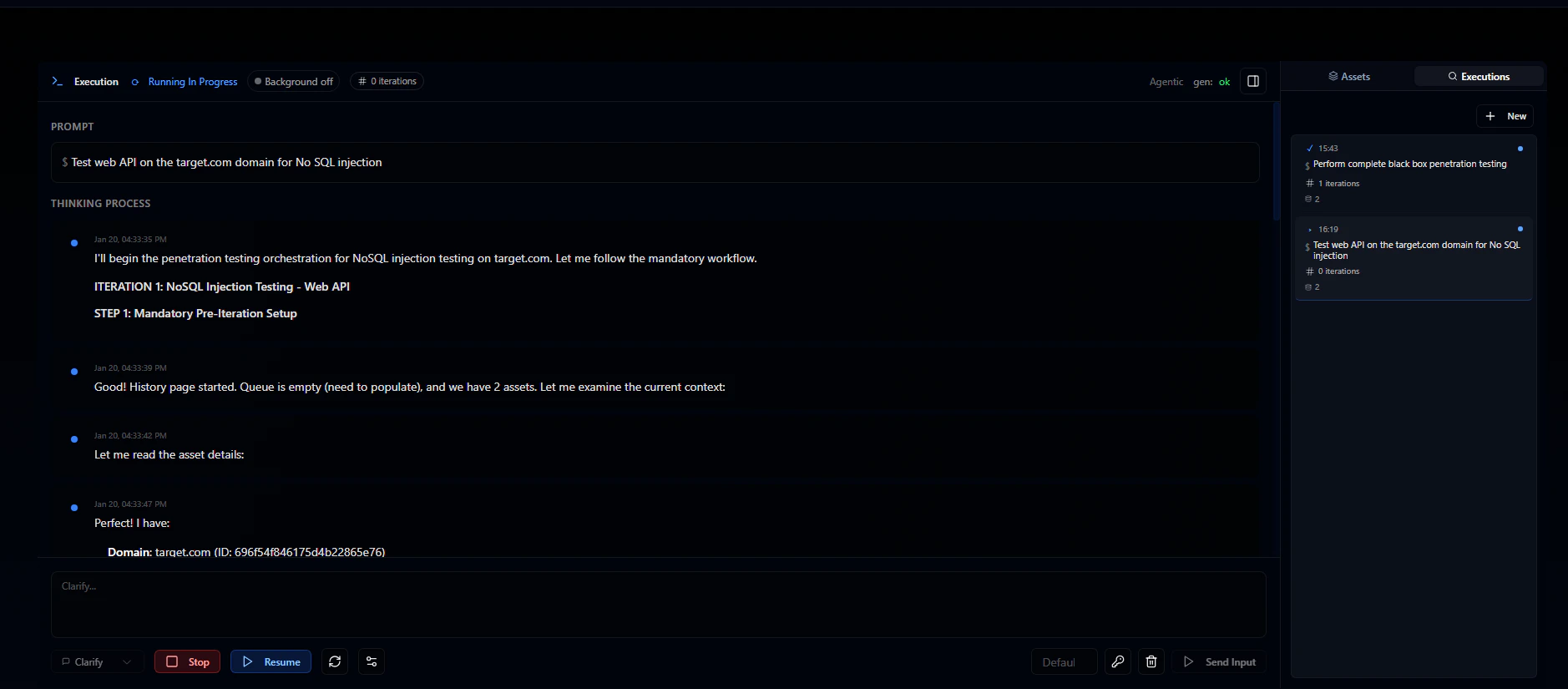
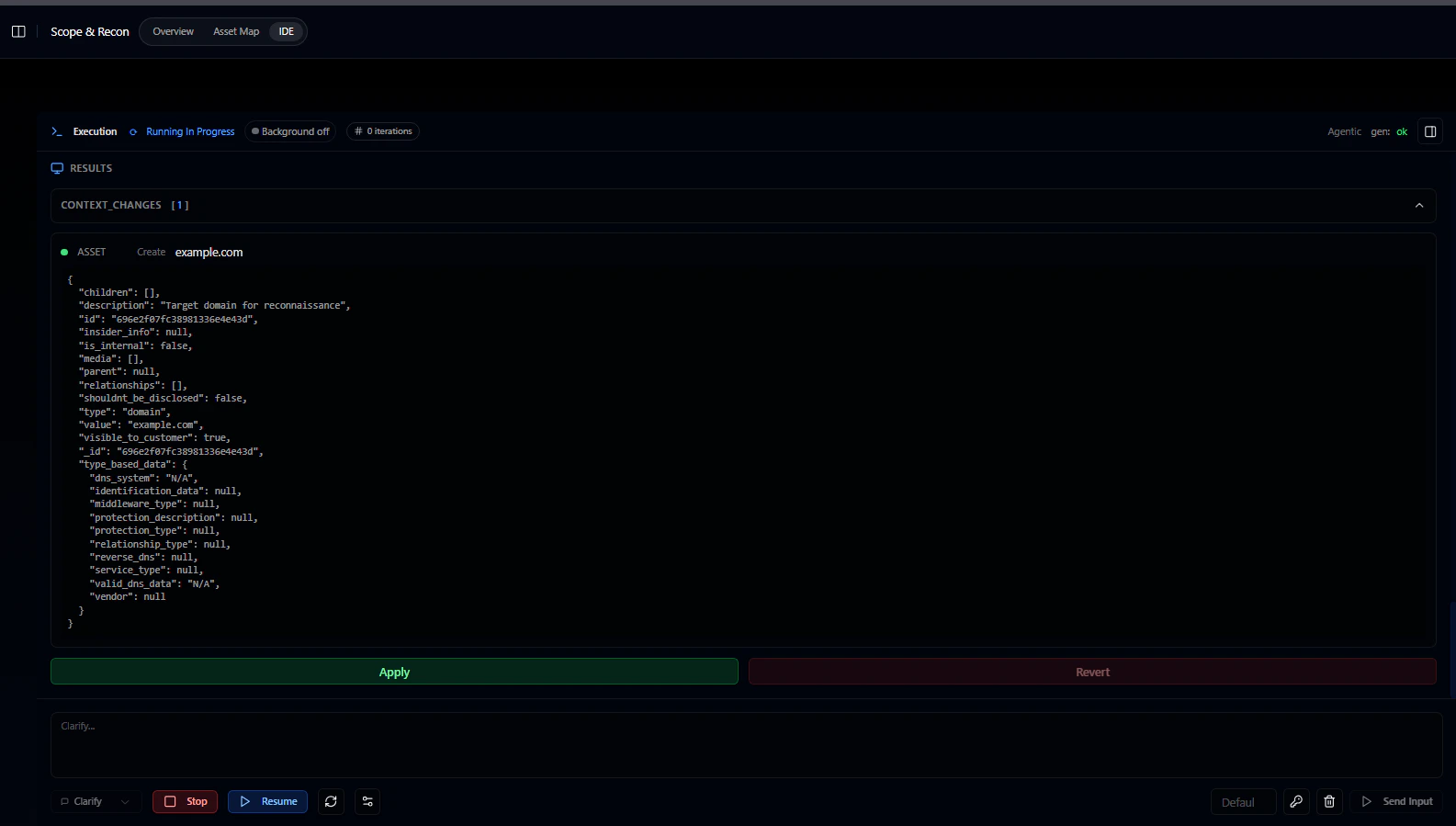
Step 4: Review results
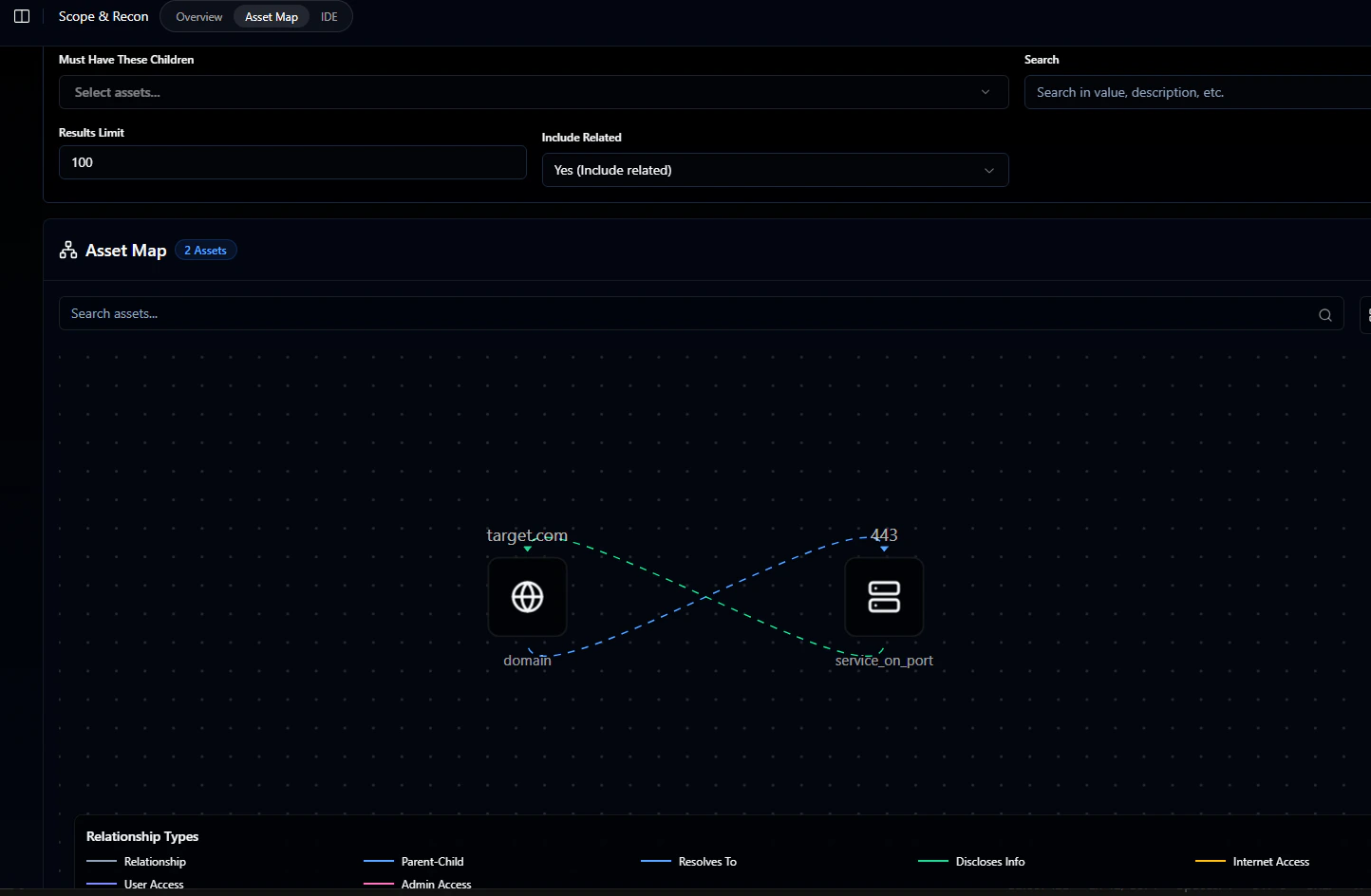
As testing runs, apply context changes periodically to sync your results. This updates the asset map and populates the vulnerability and defended attacks lists. Findings appear in the Asset map section: